Impact Dakota Blog is a blog dedicated to supporting North Dakota’s manufacturing community improve People, Purpose, Processes and Performance. Entries provide information on opportunities, new ideas, quick tips, celebrations of success, and well, frankly, anything to help you become a better manufacturer.
 Cyberattacks against manufacturing companies continue to grow.
Cyberattacks against manufacturing companies continue to grow.
 According to the U.S. Department of Homeland Security, manufacturing is the second most targeted industry based on the number of reported cyberattacks. Further, cyber criminals view small and medium-sized manufacturers (SMMs) as prime targets because many of these companies don’t have adequate preventative measures in place.
According to the U.S. Department of Homeland Security, manufacturing is the second most targeted industry based on the number of reported cyberattacks. Further, cyber criminals view small and medium-sized manufacturers (SMMs) as prime targets because many of these companies don’t have adequate preventative measures in place.
 Registration for Impacting Manufacturing Conference is now open! Make sure to register today!
Registration for Impacting Manufacturing Conference is now open! Make sure to register today!
 How many times have you just filled out a document not knowing what all the required fields meant, perhaps copying from a prior document for expediency?
How many times have you just filled out a document not knowing what all the required fields meant, perhaps copying from a prior document for expediency?
 North Dakota manufacturers are asking for
Digital Manufacturing & Design Risk Solutions.
Impact Dakota is answering your call!
North Dakota manufacturers are asking for
Digital Manufacturing & Design Risk Solutions.
Impact Dakota is answering your call!
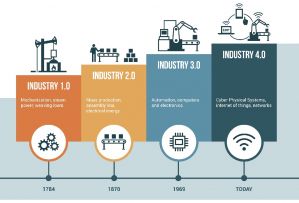
 How are small and medium-sized manufacturers (SMMs), who typically do not have the time or capital it would take to test emerging technologies, supposed to evaluate how artificial intelligence could impact their organization — and play a role in preparing them for Industry 4.0?
How are small and medium-sized manufacturers (SMMs), who typically do not have the time or capital it would take to test emerging technologies, supposed to evaluate how artificial intelligence could impact their organization — and play a role in preparing them for Industry 4.0?
 Robots have been a part of industry longer than you might think. The patent for the first industrial robot, Unimate, was granted in 1961.
Robots have been a part of industry longer than you might think. The patent for the first industrial robot, Unimate, was granted in 1961.
 New technologies and innovations continue to create manufacturing jobs.
New technologies and innovations continue to create manufacturing jobs.
 There are a number of factors why people leave their jobs. The top reason may surprise you.
There are a number of factors why people leave their jobs. The top reason may surprise you.
 Industrial Revolution 4.0 is here! Is your manufacturing business ready for the technical challenges and new risks associated with it?
Industrial Revolution 4.0 is here! Is your manufacturing business ready for the technical challenges and new risks associated with it?